They seized $4.8m in crypto… and gave away the master key online
South Korea’s National Tax Service (NTS) has found itself in the middle of a deep — and expensive — blunder after accidentally giving thieves the master key of a stolen cryptocurrency wallet.
How? Publishing is the key to access to media release, apparently for the whole world to see.
Last Thursday, the NTS issued a successful press release to the media explaining how it had taken action against 124 high-value tax evaders, and boasted of the seizure of digital assets worth 8.1 billion won – about US $5.6 million.
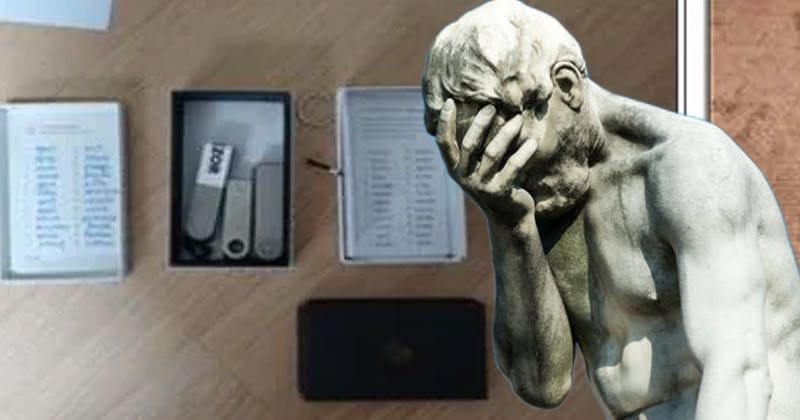
And in that press release, officials included photos of the hardware that was taken: including Ledger’s cold wallet and, sitting next to it, a handwritten note clearly showing the wallet’s memory recovery phrase.
This seed phrase is a sequence of 12 to 24 words that serves as the primary key of the cryptocurrency wallet. And as everyone with a cold hardware wallet should know, you should never share with anyone, let alone broadcast across the internet in an official press release, that seed sentence.
Early the next morning, someone had emptied the wallet of all its cryptocurrency.
For those unfamiliar with how hardware wallets work, a mnemonic phrase (or seed) is the final password for your wallet. Anyone with the phrase can restore access to that wallet on any device, anywhere in the world. And then they can transfer every last cryptocurrency token externally – without the need for physical access to the device, no PIN required, no other authentication of any kind.
Hardware wallets like Ledger are built with the assumption that the seed phrase is kept private. The whole point of “cold storage” is that the wallet’s private keys never touch the internet. When the seed phrase is exposed, offline protection is weaker than tissue.
NTS officials later explained that they had included the images in their press release to make it “more eye-catching.” Unfortunately for them, a certain press release caught the attention of some people.
The confiscated wallet in question belonged to a tax evader identified by authorities only as “Mr. C,” who had four cryptocurrency storage devices taken from his home. The hardware wallet contained about 4 million Pre-Retogeum (PRTG) tokens, worth about US$4.8 million (about 6.4 billion won) at the time.
According to a blockchain analysis by Professor Cho Jae-woo, director of the Blockchain Research Institute at Hansung University in Seoul, the theft occurred in the morning of February 27th – shortly after the press release.
Professor Cho pointed out that the original owner of the Ledger device was actually following best practice – recording the seed phrase only in a handwritten note, rather than storing it digitally. The irony, of course, is that while the tax fugitive took the necessary steps to protect his crypto wealth, the authorities tasked with protecting the seized assets did not.
So, victory for the crypto thief – yes?
Well, maybe not.
Because a thief might find it more difficult to spend his $4.8 million worth of cryptocurrency than to steal.
As Block reports, PRTG is an obscure, rarely used token. In accordance with CoinMarketCap data, recorded a volume of just US $332 in 24 hours of trading at the time of the incident and is listed on only one exchange – MEXC.
In addition the 4 million stolen tokens represent approximately 40% of PRTG’s total. Trying to convert that amount of crypto into cash will likely impact the value of the token long before the full transaction is done.
In addition, if the stolen tokens end up passing through a controlled environment with know-your-customer requirements, there is at least a chance to identify who is trying to make money from the theft.
NTS eventually issued the offending press release on its website, and issued a follow-up statement apologizing “profoundly” for what had happened.
South Korea’s National Tax Service found out the hard way. One can only hope that law enforcement agencies that seize digital assets around the world are paying attention.
After all, “don’t capture your passwords and publish them online” is a lesson most of us learned years ago.




