Cyber Security
Stay informed on the latest cybersecurity trends, tools, and best practices. Explore topics like data protection, network security, ethical hacking, and threat prevention to keep your systems safe. From beginner tips to advanced strategies, this category is your go-to resource for safeguarding against cyber threats in today’s connected world.
-

Elliptic flags crypto exchange helps Russia
Crypto exchanges that maintain active or financial ties to Russia continue to help avoid international sanctions, according to a report…
Read More » -

Digital property law is changing in the USA, China, and the UAE
Disclosure: The views and opinions expressed here are solely those of the author and do not represent the views and…
Read More » -

IoTeX confirms $2M fraud, rejects $4.3M theft claims
IoTeX reported that it contained a hack and lost around $2 million, on-chain analyst estimates put the theft at $4.3…
Read More » -

Making cloud mining a popular channel for common people to enjoy the benefits of crypto gradually
Disclosure: This article does not represent investment advice. The content and materials presented on this page are for educational purposes…
Read More » -

AI-Assisted Threat Actor Damages 600+ FortiGate Devices in 55 Countries
A Russian-speaking, financially motivated threat actor has been spotted using commercial artificial intelligence (AI) services to compromise more than 600…
Read More » -

When markets crash, traders turn to AI
Disclosure: The views and opinions expressed here are solely those of the author and do not represent the views and…
Read More » -

EC-Council Expands AI Certification Portfolio to Strengthen Readiness and Security of US AI Workforce
With $5.5 trillion in global AI risk exposure and 700,000 US workers in need of retraining, four new AI certifications…
Read More » -

‘Starkiller’ Phishing Service Proxies Real Login Pages, MFA – Krebs on Security
Most phishing websites are little more than static copies of login pages from popular sites on the Internet, and are…
Read More » -

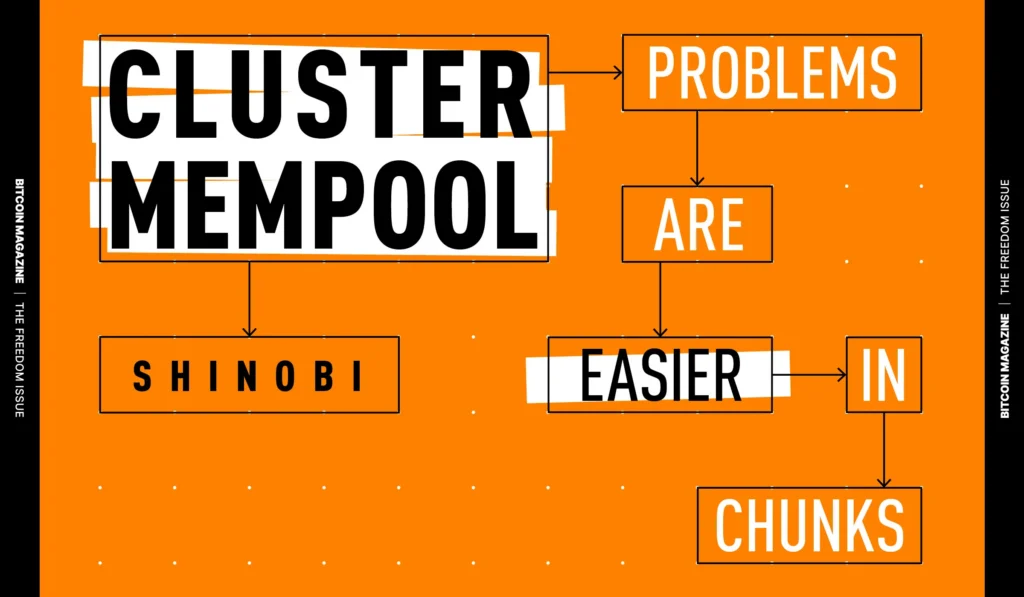
Cluster Mempool, Simple Problems with Chunks
Cluster Mempool1 is a complete reworking of how mempool handles sorting and sorting operations, conceived and implemented by Suhas Daftuar…
Read More » -

BeyondTrust Flaw Used for Web Shells, Backdoors, and Data Extrusion
IRavie LakshmananFebruary 20, 2026Vulnerability / Cyber Attacks Threat actors have been observed exploiting a disclosed critical security flaw affecting the…
Read More »