9 Best References to A Bad Requiem for Living

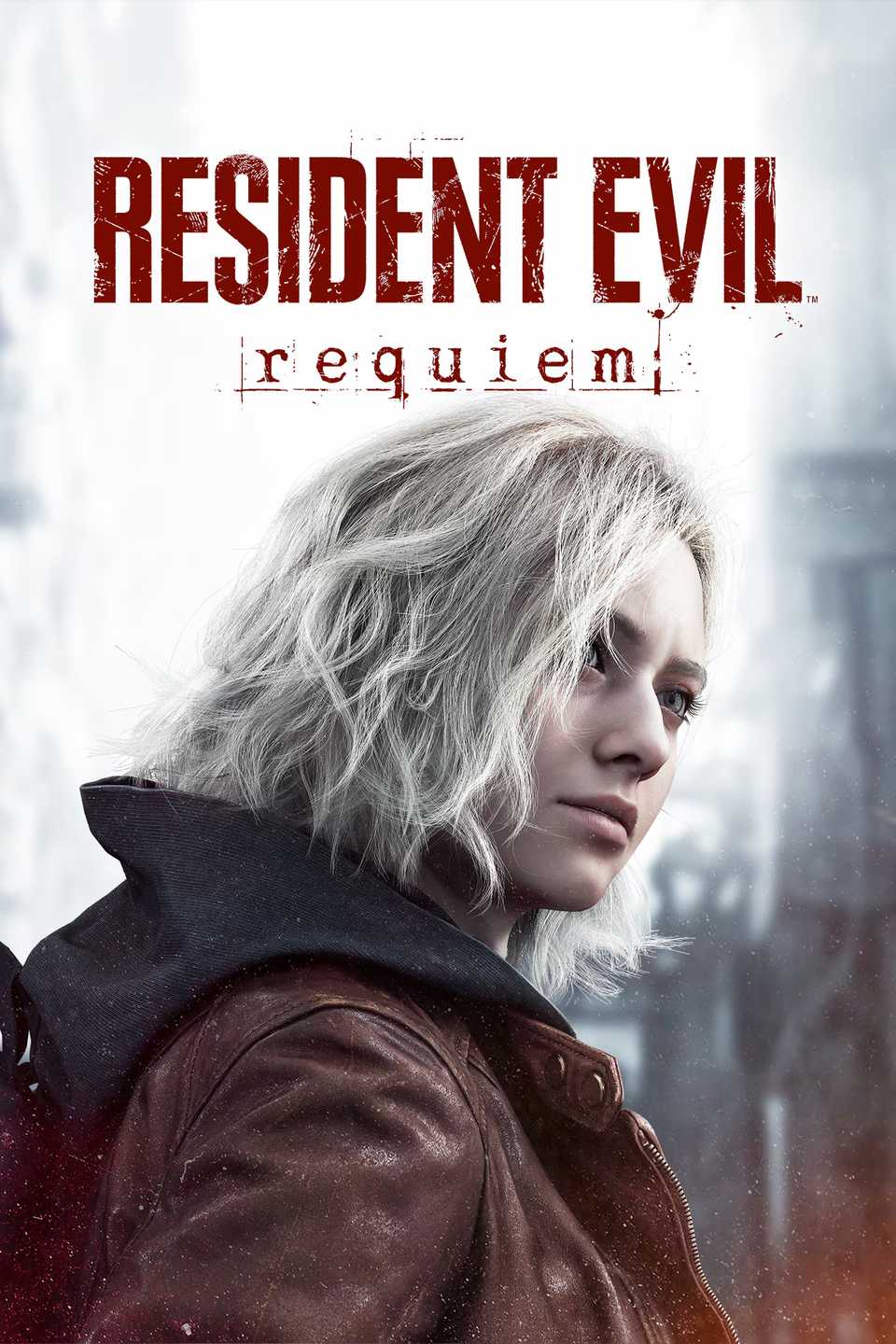
Resident Evil Requiem has a lot of secrets, and they don’t all require you to beat the game or collect a lot of challenge points to buy items from the special content store. Some of the secrets are going back to previous games in the franchise.
If you haven’t played all of the main Resident Evil games or some of the spin-off titles, you might not have caught some of Requiem’s best hits. Trust us, there are many moments, things, and details that connect Requiem Evil Requiem to previous titles in a meaningful way.
9
Zombie is looking for a snack
And He Won’t Get It
Think back to Resident Evil 2. Although there were many zombies who were interested in taking out Leon, one didn’t seem to care.
This zombie walked over to the vending machine, fixed his eyes on one of the edibles inside, and started hitting the machine, hoping it would get something out.
Years later, when you arrive at the Raccoon City Police Department, there is still a zombie hitting the vending machine. This zombie only appears when you return to the hallway, but it’s a throwback to the original game played by Leon Kennedy.
8
Hello Leon
With two L’s
The original Resident Evil 2 game had a little spelling mistake that you probably didn’t know about. When you get to the police department, there is a sign that reads “Welcome Leon,” and welcome is spelled with two L’s.
This little mistake made it into the Resident Evil 2 Remake, where the second L is found lying next to the police station. It was a fun nod to the original game.
In Resident Evil Requiem, this error gets another callback. When you enter the police station, the welcome sign can be found at the main entrance, and the lost L can be found in the west office.
7
Rising rookie Rebecca
Wesker is weird
Another throwback to the original Resident Evil 2 title is the image of Rising Rookie Rebecca. At first, this took a lot of work to figure out.
The difficulty is somewhat captured in Resident Evil Requiem, as this image gets a flashback in one of Barry’s hunts. If you read Barry’s to-do list, you will find that the book has been checked out from the library.

10 Leon Kennedy One-Liners That Somehow Make Fighting Monsters Feel Pointless
Mister Kennedy has always had the gift of the gab.
Eventually, this information will lead to you finding a note in Wesker’s office. This will then lead to a book in the library containing this image.
6
Cute Bear Charm
Ada’s name
Resident Evil 2 may have been Leon’s debut, but it wasn’t the best game he was in. Many remember Resident Evil 4 more than the second game, and a large part of that is because of Leon and Ada’s relationship.
At the end of Resident Evil 4, Ada escapes, but not before throwing Leon a set of keys. These keys have a bear charm that Leon calls cute.
In one of the few callbacks to Resident Evil 4, the Cute Bear Charm makes an appearance as one of the charms you can equip in your gear in Resident Evil Requiem. A beautiful reminder of Ada and what could have been.
5
Hunk
He always survives
Named “Hunk,” this legendary soldier is always alive and willing to do whatever it takes to complete a mission. He first appeared in Resident Evil 2, and has appeared in a few other games, but his last appearance is in Resident Evil Revelations 2.
When you join Hunk in Resident Evil Requiem, you play the role of a boss, which requires you to defeat him in order to advance the story. Don’t worry, his story may not end here.
If you leave the boss room after defeating Hunk and come back, you will see that his body is gone. This is a big callback to him who always survived the job, and leaves the door open for his return.
4
X I will give it to Ya
Another Dictator has appeared
Mr. X is one of those contrarians who all remember. Well, at least those who played Resident Evil 2 remember him and how he can wreak havoc on your gameplay if you’re not careful.
Don’t worry, Mr. X isn’t back in Resident Evil Requiem, but a dictator who looks exactly like him is, and he’s messing with Leon. What makes this flashback even better is that Leon seems concerned about Tyrant’s appearance.

10 Resident Evil Need Mechanics That Make Combat Feel More Desperate Than Ever
Being surrounded by dead bodies is depressing, who knew?
When the boss fight starts, Leon even says that he can keep the world safe from monsters like Mr. X wannabe.
3
Links
Making Links
Revealed at the end of Resident Evil Requiem, Zeno and Victor Gideon are working with The Connections – an international criminal organization specializing in the use of bioweapons.
In Resident Evil 7, Connections is revealed, and it is shown that the group confronts Eveline again, the Baker House incident.
This reboot shows that The Connections are a bigger threat than first thought. Well, we’ll have to see where it goes now that both Zeno and Gideon are dead, and Elpis has been freed.
2
Wolves
Here Comes Chris
The Hound Wolf Squad makes an appearance at the end of Resident Evil Requiem, and is a throwback to many games in the series. Especially Resident Evil 7 and Resident Evil Village.
Chris Redfield created this select group after the BSAA covered up the Baker House Incident and covered up their failure to kill Eveline. That being said, the Hound Wolf Squad has made an appearance in the last two games in the series.
Now that it’s been confirmed that they’re in Resident Evil Requiem, it’s only a matter of time before Chris shows up again. Maybe he’ll teach Leon how to drill through rocks.
1
Kendo
A Very Sad Moment
In Resident Evil 2, you get to meet the owner of the Kendo Gun Shop. It turns out that his daughter is infected, and he gets to listen to gunshots.
It is by far the saddest moment in all of the Resident Evil games, and one that has stuck with many over the years. This time we get an emotional call after passing through the police department.
Leon sees the remains of the man and his daughter and is reminded that he could do nothing to save them. It’s another moment that will definitely be remembered for years to come.

Resident Evil: 10 Tips and Tricks When Playing as Leon
When you play Resident Evil Requiem, you play between Grace and Leon. Leon is meant to be full of things, here are some ways to make it more fun.
- Released
-
February 27, 2026
- The ESRB
-
Mature 17+ / Strong Violence, Blood and Gore, Strong Language, In-Game Purchases












