Who is Kimwolf Botmaster “Dort”? – Krebs on Security
In early January 2026, KrebsOnSecurity revealed how a security researcher disclosed a vulnerability that was used to build. Kimwolfthe largest and most disruptive botnet in the world. Since then, the person who controls Kimwolf – who goes by the handle “Dort” — has orchestrated a series of distributed denial-of-service (DDoS) attacks, doxing and email flooding attacks on the researcher and author, and recently resulted in a SWAT team being sent to the researcher’s home. This post examines what is known about Dort based on public information.
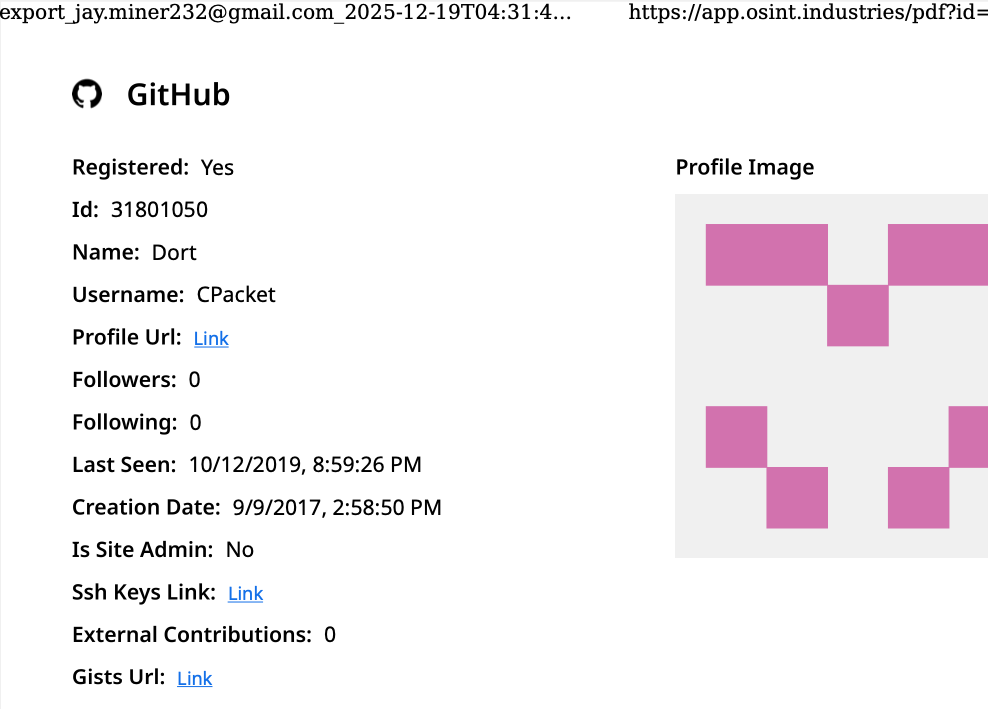
A public “dox” created in 2020 asserted that Dort was a Canadian teenager (DOB August 2003) who used the alias “CPacket” and “M1ce.” CPacket username search on open source intelligence OSINT Industries you get a GitHub an account under the names Dort and CPacket created in 2017 using an email address jay.miner232@gmail.com.
Photo: osint.industries.
Internet intelligence company Intel 471 says jay.miner232@gmail.com was used between 2015 and 2019 to create accounts on multiple cybercrime forums, including It is nulled (username “Ubuntu”) and It is cracked (user “Dorted”); Intel 471 reports that both of these accounts were created from the same Internet address in Rogers Canada (99.241.112.24).
Dort was a very active player in the Microsoft game Minecraft the famous “Dortware” software that helps players cheat. But somewhere, Dort graduated to hacking Minecraft games to allow more serious crimes.
Dort also used a nickname DortDevthe identity that operated in March 2022 on the chat server of a powerful cybercriminal group known as LAPSUS$. Dort sold a temporary email address registration service, along with a code called “Dortsolver,” that could bypass various CAPTCHA services designed to prevent automated account abuse. Both offerings were announced in 2022 SIM Landphone station dedicated to SIM replacement and account takeover service.
Internet intelligence company A bright point indexed 2022 on Dort’s SIM Land indicating that this person has created an email that can also be used to pass CAPTCHA facilities with the help of another hacker who went by the handle “Qoft.”
“I’m officially working with Jacob,” Qoft said in 2022 in response to another user, referring to their special business partner Dort. In the same interview, Qoft bragged that the pair had stolen more than $250,000 from Microsoft Xbox Game Pass accounts by creating a system that created multiple Game Pass identities using stolen payment card data.
Who does Jacob Qoft call their business partner? Breach tracking service Constella Intelligence finds the password used by jay.miner232@gmail.com has been used by just one other email address: jacobbutler803@gmail.com. Remember that Dort’s 2020 dox said their birth date was August 2003 (8/03).
Searching for this email address at DomainTools.com reveals that it was used in 2015 to register Minecraft-themed domains, all assigned to Jacob Butler in Ottawa, Canada with an Ottawa phone number of 613-909-9727.
Constella Intelligence finds that jacobbutler803@gmail.com was used to register an account on the nulled hacker forum in 2016, and the account name “M1CE” in Minecraft. Leaving the password used for their account Nulled indicates that email addresses have been shared jayminer232@gmail.com again jbutl3@ocdsb.cathe last is an address in the domain of Ottawa-Carelton District School Board.
The data is identified by a breach tracking service Spycloud suggests that at some point Jacob Butler shared a computer with his mother and his sibling, which may explain why their email accounts are linked to the password “jacobsplugs.” Neither Jacob nor any of the Butler family members responded to requests for comment.
An open source intelligence service Epieos finds jacobbutler803@gmail.com created a GitHub account “MemeClient.” Meanwhile, Flashpoint pointed to an anonymous Pastebin.com post that has since been deleted from 2017 announcing that MemeClient was the creation of a user named CPacket – one of Dort’s original developers.
Why is Dort so mad? On January 2, KrebsOnSecurity published Kimwolf Botnet is Stalking Your Local Network, which examined research on the botnet by. Benjamin Brundagefounder of proxy tracking service The Synthient. Brundage discovered that Kimwolf botmasters were exploiting a little-known weakness in residential proxy services to infect poorly protected devices — such as TV boxes and digital picture frames — connected to internal, private networks of proxy endpoints.
By the time that story went live, most of the affected proxy providers had been notified by Brundage and had fixed the vulnerability in their systems. That remediation process greatly reduced Kimwolf’s ability to spread, and within hours of the story being published Dort created a Discord server in my name that began publishing personal information about violent threats against Brundage, Yours Truly, and others.

Dort and friends blamed themselves for organizing a swatting attack on a public Discord server.
Last week, Dort and friends used the same Discord server (then named “Krebs’s Koinbase Kallers”) to threaten Brundage with an attack, reposting his home address and personal information. Brundage told KrebsOnSecurity that local police then visited his home in response to a scam that occurred when a server member posted a door emoji and taunted Brundage.
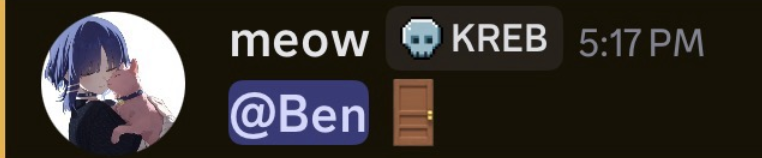
Dort, who goes by the name “Meow,” taunts Synthient’s founder Ben Brundage with a photo of the door.
Someone on the server then linked to a new appropriate (and NSFW) Soundcloud diss track recorded by user DortDev that included a sticky message from Dort that read, “Ur dead nigga. u better watch ur fucking back. sleep with one eye open. bitch.”
“A great shilling for a new front door,” says the diss track. “If his head is blown off by SWAT officers. What’s it like not having a front door?”
With any luck, Dort will soon be able to tell us all what it’s like.




