Anti-DDoS Firm Heaped Attacks on Brazilian ISPs – Krebs on Security

A Brazilian technology company specializing in protecting networks from distributed denial-of-service (DDoS) attacks has been allowing a botnet responsible for an extended campaign of massive DDoS attacks against some network operators in Brazil, KrebsOnSecurity has learned. The company’s chief executive says that the brutal act was caused by a security breach and may have been the work of a competitor trying to discredit his company in the public eye.
Archer AX21 router from TP-Link. Photo: tp-link.com.
Over the past few years, security experts have tracked a series of massive DDoS attacks originating in Brazil and targeting only Brazilian ISPs. Until recently, it was unclear who or what was behind this digital siege. That changed earlier this month when a trusted source who asked not to be identified shared a curious file archive that was revealed in an open directory online.
The leaked archive contained several Portuguese-language malicious programs written in Python. It also included the CEO’s private SSH authentication keys Large networksa Brazilian ISP that primarily provides DDoS protection for other Brazilian network operators.
It was founded in Miami, Fla. In 2014, Huge Networks’ operations focused on Brazil. The company evolved from protecting game servers from DDoS attacks and evolved into an ISP-focused DDoS mitigation provider. It does not appear in any public abuse complaints and is not associated with any known DDoS-for-hire services.
However, the exposed archive shows that a Brazilian-based threat actor has maintained root access to the infrastructure of Huge Networks and built a powerful DDoS botnet by mass scanning the Internet to find unsecured Internet routers and unmanaged domain name system (DNS) servers on the web that can be included in the attack.
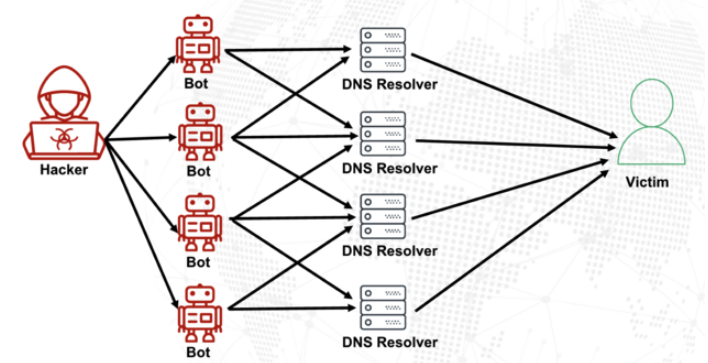
DNS is what allows Internet users to access websites by typing in standard domain names instead of relative IP addresses. Ideally, DNS servers only provide answers to machines within a trusted domain. But so-called “DNS reflection” attacks rely on DNS servers (mis)configured to receive queries from anywhere on the web. Attackers can send spoofed DNS queries to these servers so that the request appears to be coming from the target’s network. That way, when the DNS servers respond, they respond to the spoofed (target) address.
By using an extension of the DNS protocol that allows large DNS messages, botmasters can significantly increase the size and impact of virtual attacks – making DNS queries so that responses are much larger than requests. For example, an attacker can write a DNS request of less than 100 bytes, delivering a response 60-70 times larger. This amplification effect is especially felt when the perpetrators can query many DNS servers with these fake requests from tens of thousands of compromised devices at the same time.
DNS amplification and logic attacks, demonstrated. Photo: veracara.digicert.com.
The leaked file archive includes a command-line log that shows exactly how this attacker built and maintained a powerful botnet by exploring the Internet TP-Link Archer AX21 routes. Specifically, the botnet targets TP-Link devices that remain vulnerable to CVE-2023-1389, an unverified command injection vulnerability that dates back to April 2023.
Malicious domains in the exposed Python attack scripts include hikylover’s DNS lookup[.]st, and c.loyaltyservices[.]lol, both domains were flagged last year as control servers for an Internet of Things (IoT) botnet powered by a variant of the Mirai malware.
The leaked archive shows that the botmaster linked its scans from a Digital Ocean server flagged for exploit activity hundreds of times over the past year. Python scripts request many Internet addresses provided by Large Networks that have been used to identify targets and execute DDoS campaigns. The attack was strictly limited to the range of Brazilian IP addresses, and documentation shows that the beginning of each selected IP address was attacked for 10-60 seconds by four identical processes per host before the botnet moved on to the next target.
The archive also shows these malicious Python scripts that rely on the SSH private keys of the CEO of Huge Networks, Erick Nascimento. Contacted for comment about the files, Mr. Nascimento said he did not write the attack plans and did not realize the extent of the DDoS campaigns until he was contacted by KrebsOnSecurity.
“We have discovered and notified many Tier 1 executives about massive DDoS attacks on small ISPs,” Nascimento said. “We didn’t go deep enough then, and what you sent makes that clear.”
Nascimento said the unauthorized activity may be related to digital intrusions first discovered in January 2026 that compromised two of the company’s development servers, as well as his personal SSH keys. But he said there was no evidence those keys were used after January.
“We notified the team in writing that same day, cleared the boxes, and keyed in,” Nascimento said, sharing a screenshot of the January 11 notice from Digital Ocean. “Everything is written inside.”
Mr. Nascimento said Huge Networks has since engaged a third-party network firm to investigate further.
“Our active assessment so far is that this all started with a single internal compromise — a single pivot point that gave the attacker downstream access to other resources, including my legacy drop,” he wrote.
“The compromise happened with a bastion/jump server that few people had access to,” Nascimento continued. “Digital Ocean marked the droplet on January 11 – vulnerable due to SSH key leak, in their words – I was traveling at the time and mentioned it when I returned.
The malicious software that powers the botnet of TP-Link devices used in DDoS attacks on Brazilian ISPs is based on Mirai, a type of malware that first came to public attention in September 2016 by launching a devastating DDoS attack that took this website offline for four days. In January 2017, KrebsOnSecurity identified the authors of Mirai as co-owners of a DDoS mitigation firm that was using a botnet to attack game servers and scare off new customers.
In May 2025, KrebsOnSecurity was hit by another DDoS on Mirai that Google called the biggest attack it had ever mitigated. That report involved a 20-year-old Brazilian man who ran a DDoS mitigation company and several DDoS-for-hire services that have since been seized by the FBI.
Nascimento has categorically denied being involved in DDoS attacks with Brazilian operators to establish his company’s services business.
“We do not launch DDoS attacks against Brazilian users to sell protection,” Nascimento wrote in response to questions. “Our sales model is very penetrating and by combining the channel, distributors, partners – not an active look based on market events. The targets in the documents you received are small regional suppliers, most of whom are not in our customers or in our sales line – a fact confirmed by public sources such as QRator.”
Nascimento insists that he has “strong evidence stored on the blockchain” that this was all done by a competitor. As for who that competitor is, the CEO won’t say.
“I would like to share this with you, but it could not be published as it would lose something surprising to my unfaithful opponent,” he explained. “Coincidence or not, your contact happened a week before an important event – one that this contestant has NEVER participated in (and it’s a regular event in this industry). And this year, they will be participating. Amazing, right?”
Which is really weird.




