Russian Routers Hacked To Steal Microsoft Office Tokens – Krebs on Security

Hackers linked to a Russian military intelligence unit are exploiting known flaws in old Internet routers to harvest dozens of emerging authentication tokens. Microsoft Office users, security experts warned today. The espionage campaign allowed state-backed Russian hackers to silently issue authentication tokens to users on more than 18,000 networks without installing any malicious software or code.
Microsoft said in a blog post today that it identified more than 200 organizations and 5,000 consumer devices that were caught by a subtle but incredibly simple surveillance network created by a Russian-backed threat actor known as “Forest Blizzard.”
How the target DNS requests are redirected to the router. Photo: Black Lotus Labs.
Also known as APT28 and Fancy Bear, Forest Blizzard was developed by military intelligence units within Russia’s General Staff Main Intelligence Directorate (GRU). APT 28 compromised Hillary Clinton’s campaign, the Democratic National Committee, and the Democratic DRM Campaign Committee in 2016 in an attempt to disrupt the US presidential election.
Researchers at Black Lotus Labsthe security department of an Internet backbone provider Lumenfound that at the peak of its activity in December 2025, Forest Blizzard’s surveillance net trapped more than 18,000 Internet routers that were either severely unsupported, end-of-life routers, or otherwise far from security updates. A new report from Lumen says hackers primarily target government agencies—including the foreign service, law enforcement, and third-party email providers.
Black Lotus Security Engineer Ryan English said the GRU hackers did not need to install malware on the targeted routers, which were too old Mikrotik again TP-Link devices marketed to the Small Office/Home Office (SOHO) market. Instead, they used known vulnerabilities to modify the Domain Name System (DNS) settings of routers to include DNS servers controlled by cybercriminals.
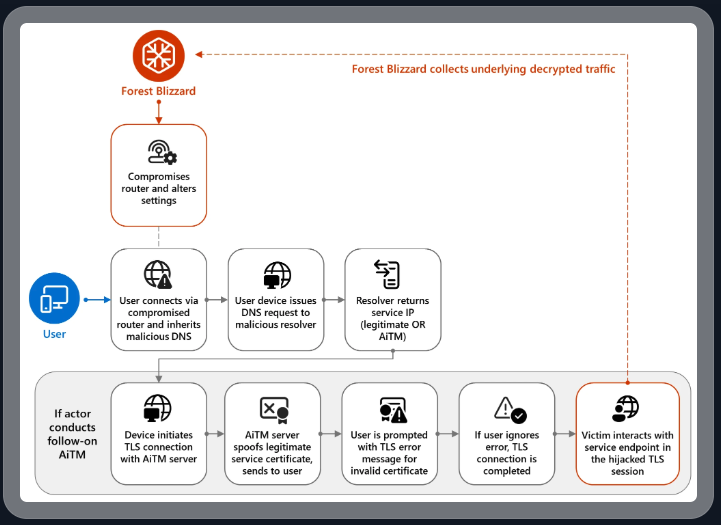
Like in the UK National Cyber Security Center (NCSC) notes in a new advisory detailing how Russian cyber actors have been compromising routes, the DNS that allows people to access websites by typing in generic addresses, instead of relative IP addresses. In DNS hijacking attacks, bad actors disrupt this process to secretly send users to malicious websites designed to steal login credentials or other sensitive information.
English said the routers attacked by Forest Blizzard were reprogrammed to use DNS servers that point to a number of secret servers controlled by the attackers. Essentially, attackers can broadcast their malicious DNS settings to all users on the local network, and from there on intercept any OAuth authentication tokens sent by those users.
DNS hijacking through router compromise. Image: Microsoft.
Because those tokens are usually transferable only after user has successfully logged in and gone through multi-factor authentication, attackers can gain direct access to victim accounts without stealing individual user credentials and/or one-time codes.
“Everybody’s looking for a piece of malware that’s going to dump something on your cell phone or something,” English said. “These guys didn’t use malware. They did it the old-school, gray-beard way that doesn’t really shine but gets the job done.”
Microsoft refers to the Forest Blizzard activity as using DNS hijacking to “support post-compromise adversary-in-the-middle (AiTM) attacks on Transport Layer Security (TLS) connections against Microsoft Outlook web domains.” The software giant said that while targeting SOHO devices is not a new tactic, it is the first time Microsoft has seen Forest Blizzard use “DNS hijacking at scale to support AiTM TLS communication after exploiting edge devices.”
Developed by Black Lotus Labs Danny Adamitis said it will be interesting to see how Forest Blizzard responds to today’s focus on their intelligence operations, noting that the group quickly changed its tactics in response to a similar NCSC report (PDF) in August 2025. At the time, Forest Blizzard was using malware to control a highly targeted and small group of vulnerable routers. But Adamitis said the day after the NCSC report, the group quickly abandoned the malware approach in favor of mass modification of DNS settings on thousands of vulnerable routers.
“Before the final NCSC report came out they used this capability in limited circumstances,” Adamitis told KrebsOnSecurity. “After the report was released they used the skill in a systematic way and used it to identify everything that was at risk.”
TP-Link was among the router makers facing a total ban in the United States. But on March 23, the US Federal Communications Commissionn (FCC) took a broader approach, announcing that it would no longer approve consumer-grade Internet routers manufactured outside the United States.
The FCC has warned that foreign-made routers have become an uncontrollable national security threat, and that poorly secured routers pose “a serious Internet security risk that could be exploited quickly and significantly disrupt US critical infrastructure and directly harm US people.”
Experts have argued that few new consumer-grade routers will be available for purchase under this new FCC policy (with the possible exception of Musk’s Starlink satellite Internet routers, which are manufactured in Texas). The FCC says router makers can apply for special “conditional authorization” from the Department of Defense or the Department of Homeland Security, and that the new policy does not affect any consumer-grade routers previously purchased.




